School districts are under increasing pressure to make smarter decisions about programs, products, and investments. Leaders want to know what is improving student outcomes, where resources are working, and what should change next. That is where a strong education program evaluation becomes valuable.
But many district leaders share a reasonable concern: can you evaluate programs without putting sensitive student information at risk?
The answer should be yes.
Districts should never have to choose between protecting student privacy and learning what works for students. Strong evaluation studies can do both. With disciplined data minimization, secure storage, limited access, de-identification, and careful reporting, schools can gain useful evidence while honoring legal and ethical obligations.
The real choice is not privacy or insight. It is a careless evaluation versus a responsible evaluation.
Why Student Privacy Matters in Every Evaluation Study
Student privacy matters for at least three reasons.
First, it is a legal responsibility. Laws and regulations, such as FERPA, govern how education records can be accessed, shared, and disclosed. The U.S. Department of Education’s Student Privacy Policy Office provides guidance on how schools should handle protected student records and disclosures.
Second, it is an ethical responsibility. Families trust schools with highly sensitive information about children, including academic performance, attendance, behavior, and personal identifiers. That trust should be treated seriously.
Third, it is a strategic responsibility. If staff, families, or community members do not trust how the district handles data, even valuable studies can face resistance.
Evidence loses value quickly when trust is lost first.
Phase 1: Gathering Only the Data You Truly Need
The strongest privacy strategy often begins before any file is transferred.
When conducting program evaluation for school districts, organizations should collect only the student information truly needed to answer the research question. If the goal is to understand whether a literacy program improved reading scores, the study may need assessment data, grade level, and participation status. It may not need names, addresses, or unnecessary demographic fields.
Best practices include:
- Collect only fields necessary for the evaluation
- Avoid direct identifiers unless essential
- Use clear notices and consent procedures when required
- Define the purpose before requesting data
Too many organizations assume more data leads to better decisions. In reality, excessive data collection creates burden and risk. Useful evaluation starts with precision.
Phase 2: Storing and Managing Data Securely
Once data is received, security discipline matters.
Strong secure student data practices include storing files in protected environments with access limited to staff who have a legitimate need to work with the data. The National Institute of Standards and Technology publishes best practices related to encryption, password protection, and access controls that are widely used across sectors.
Districts and evaluation partners should consider:
- Encryption during transfer and storage
- Strong passwords and multi-factor authentication
- Role-based access controls
- Limited permissions for authorized personnel only
- Written data-sharing agreements
- Clear retention and destruction timelines
The safest student record is the one that only the right people can access for the right reason.
This is especially important when districts work with outside vendors that offer school program evaluation or education data analysis services.
Phase 3: Analyzing Data Without Exposing Identities
Many people assume useful analysis requires named student records. It often does not.
High-quality studies can frequently rely on de-identified or pseudonymized data, where names and direct identifiers are removed and replaced with anonymous IDs. That allows analysts to examine trends and compare groups while reducing exposure risk.
Best practices include:
- De-identify records whenever possible
- Use anonymous IDs instead of names
- Work with the smallest dataset needed
- Limit highly specific combinations of characteristics
- Watch for small subgroup re-identification risk
For example, if a subgroup includes only two students in a grade level at one campus, reporting detailed results may unintentionally reveal identities.
The National Center for Education Statistics has long emphasized suppression methods and disclosure protections when publishing sensitive education data.
Privacy and rigor can coexist. Strong independent program evaluation for K–12 does not require reckless handling of records.
Phase 4: Reporting Results Responsibly
The final stage of an evaluation is often the most visible. It is also where careless reporting can undo careful handling earlier in the process.
Public-facing findings should focus on patterns, outcomes, and actionable insight rather than student-level detail.
Responsible reporting often includes:
- Aggregate results instead of individual records
- Suppression of small cells
- Removal of names and ID numbers
- Careful review of charts and tables
- Avoiding anecdotes that could identify students
Stakeholders need trends, not student identities.
A strong education program impact report helps leaders understand what happened without exposing who experienced it.
A Simple Rule for Every Phase
Across collection, storage, analysis, and reporting, one practical rule applies:
Collect Less. Only gather what is needed.
Share Less. Limit access to authorized parties.
Restrict More. Use permissions, contracts, and controls.
This approach supports student data privacy in schools while keeping evaluation practical and low burden.
How MomentMN Snapshot Reports Prioritize Student Privacy

For districts considering external evaluation support, privacy practices matter as much as methodology.
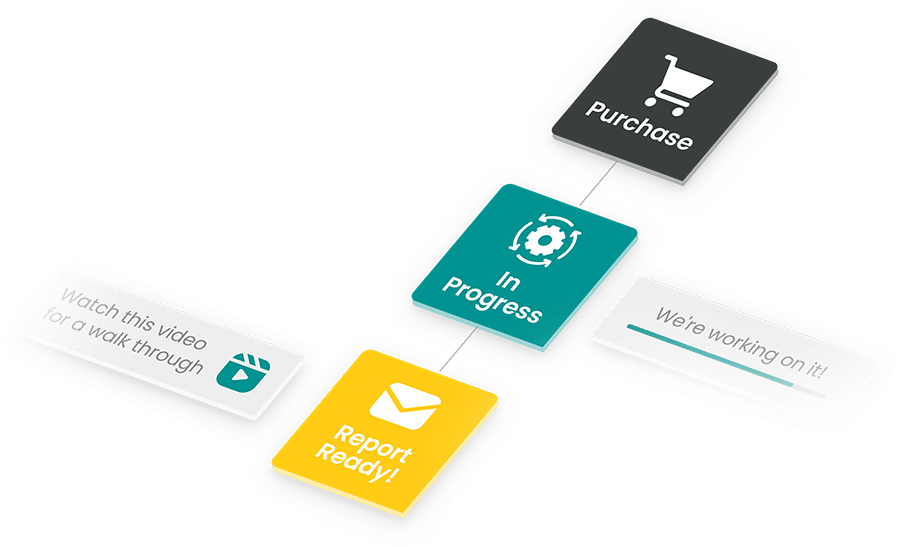
MomentMN Snapshot Reports are designed to provide rigorous evidence while minimizing privacy risk and internal burden.
Their privacy approach includes:
- Secure data sharing by participating districts
- Storage on offline, encrypted, password-protected computer systems
- Access restricted only to staff producing reports
- Standardized suppression rules in reporting
- No identifying information, including district names, displayed on reports
- Permanent data destruction when service ends
- Data-sharing agreements restricting use solely to the agreed evaluation purpose
Independent evaluation should reduce burden, not create new risk.
Privacy Protection Makes Better Decisions Possible
When districts trust the process, they are more willing to evaluate tools, programs, and investments. That leads to stronger budgeting decisions, smarter renewals, and clearer priorities.
Privacy is not a barrier to evidence-based decision-making in schools. It is part of doing it correctly.
Strong evaluation allows leaders to ask:
- Is this program improving outcomes?
- Which students are benefiting most?
- Where should we invest next?
- What should we change or stop funding?
Those answers become easier to pursue when privacy protections are clear from the beginning.
Protecting Students Includes Protecting Their Data
Schools work hard to protect students in classrooms, hallways, buses, and online spaces. Their information deserves the same seriousness.
The best evaluation partners help districts learn what works while keeping privacy central at every step.
Want independent impact evidence without creating extra burden or privacy concerns? Request a MomentMN Snapshot Report and see how a secure, privacy-conscious evaluation can deliver clear answers using existing district data.